Verifying the Host Key
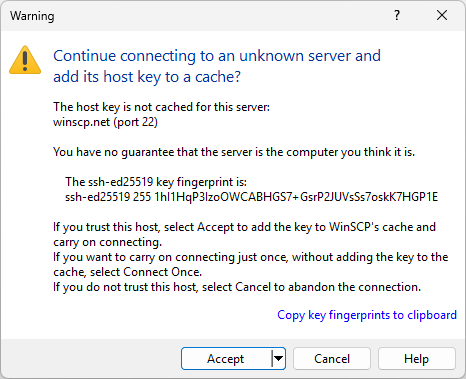
If you are using WinSCP to connect to a server for the first time, you will probably see a message looking something like this:
This is a feature of the SSH protocol. It is designed to protect you against a network attack known as spoofing: secretly redirecting your connection to a different computer, so that you send your password to the wrong machine. Using this technique, an attacker would be able to learn the password that guards your login account, and could then log in as if they were you and use the account for their own purposes.
Advertisement
To prevent this attack, each server has a unique identifying code, called a host key. These keys prevent a server from forging another server’s key. If you connect to a server and you receive an unexpected host key, WinSCP can warn you that the server may have been switched and that a spoofing attack might be underway.
WinSCP records the host key for each server you connect to, in the configuration storage. Every time you connect to a server, it compares the server’s host key to the host key you received the last time you connected. If the keys differ, you will receive a warning and a chance to abandon your connection before you enter any private information such as a password.
However, when you connect to a server for the first time, WinSCP has no way of telling whether the host key is the right one or not. So it gives the warning shown above, and asks you whether you want to trust this host key or not.
Whether or not to trust the host key is your choice. If you are connecting within a company network, you might feel that all the network users are on the same side and spoofing attacks are unlikely, so you might choose to trust the key without checking it. If you are connecting across a hostile network (such as the Internet), you should check with your system administrator, perhaps by telephone or in person. (When verifying the fingerprint, be careful with letters and numbers that can be confused with each other: 0/O, 1/I/l, and so on.)
Many servers have more than one host key. If the system administrator sends you more than one fingerprint, you should make sure the one WinSCP shows you is on the list, but it doesn’t matter which one it is.1 See, what are other ways to obtaining host key fingerprint.
System administrator can restrict connection to server without having their host keys accepted in advance.
Do not confuse host public key with your private/public key pair used for authentication.
Displaying Host Key
Once the key is verified, you can see it during all future sessions on Server and Protocol Information Dialog.
Advertisement
Automating Host Key Verification
Learn how to accept host key automatically in script.
In .NET assembly, use SessionOptions.SshHostKeyFingerprint. You can use the Session.ScanFingerprint method to retrieve the server’s host key fingerprint to allow a user to manually verify the key, before you assign the fingerprint to the SessionOptions.SshHostKeyFingerprint.
- The text is copy of PuTTY User Manual or was inspired by it.Back