Hi Martin,
So how AWS works is that your IAM user can have multiple IAM roles, sometimes in different AWS accounts. Scenario: I have an user created in AWS account A, but I want to access a bucket in account B.
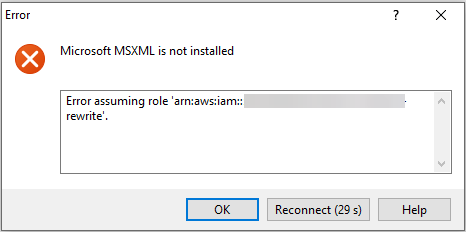
One achieves this by authenticating with AWS using the various credentials, and then assuming a role in account B. As
@fabiopedrosa described, the access ID and secret key (Account A) gets read from
.aws/credentials, but the
role_arn (the role in Account B we want to assume) is stored in
.aws/config (
role_arn). The respective API call for assuming a role is described here:
https://docs.aws.amazon.com/STS/latest/APIReference/API_AssumeRole.html
It is also important to note that this role is attached to the IAM user. I am not talking about the EC2 instance's instance role which was implemented in
Issue 2089 – Allow S3 connection with IAM role instead of credentials.